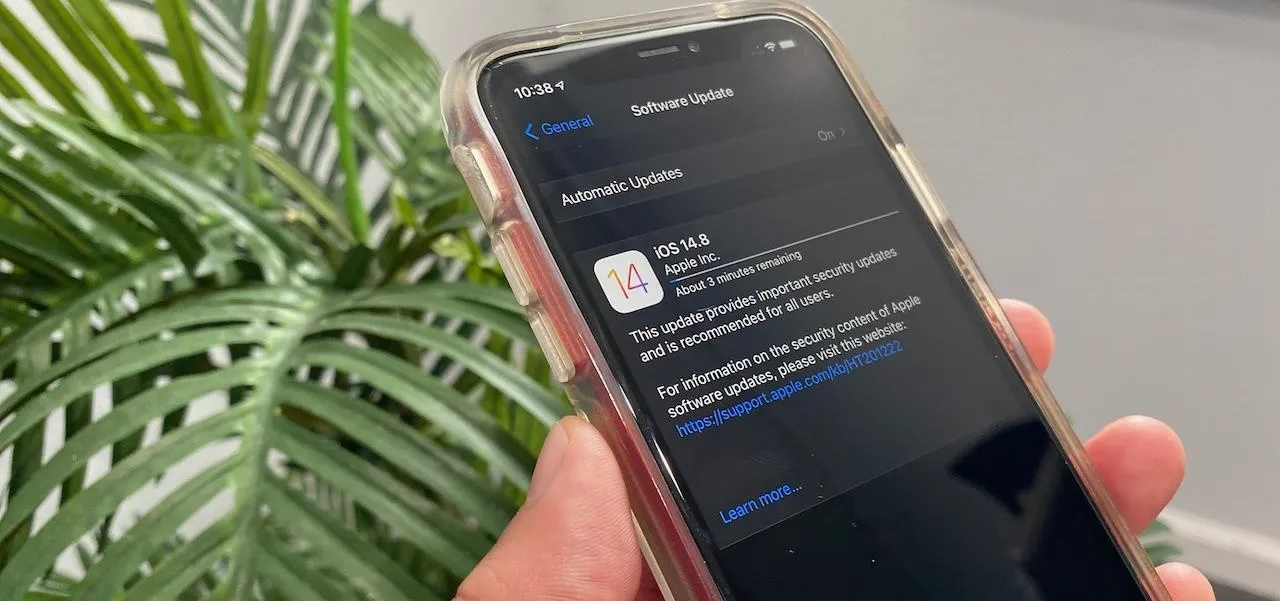
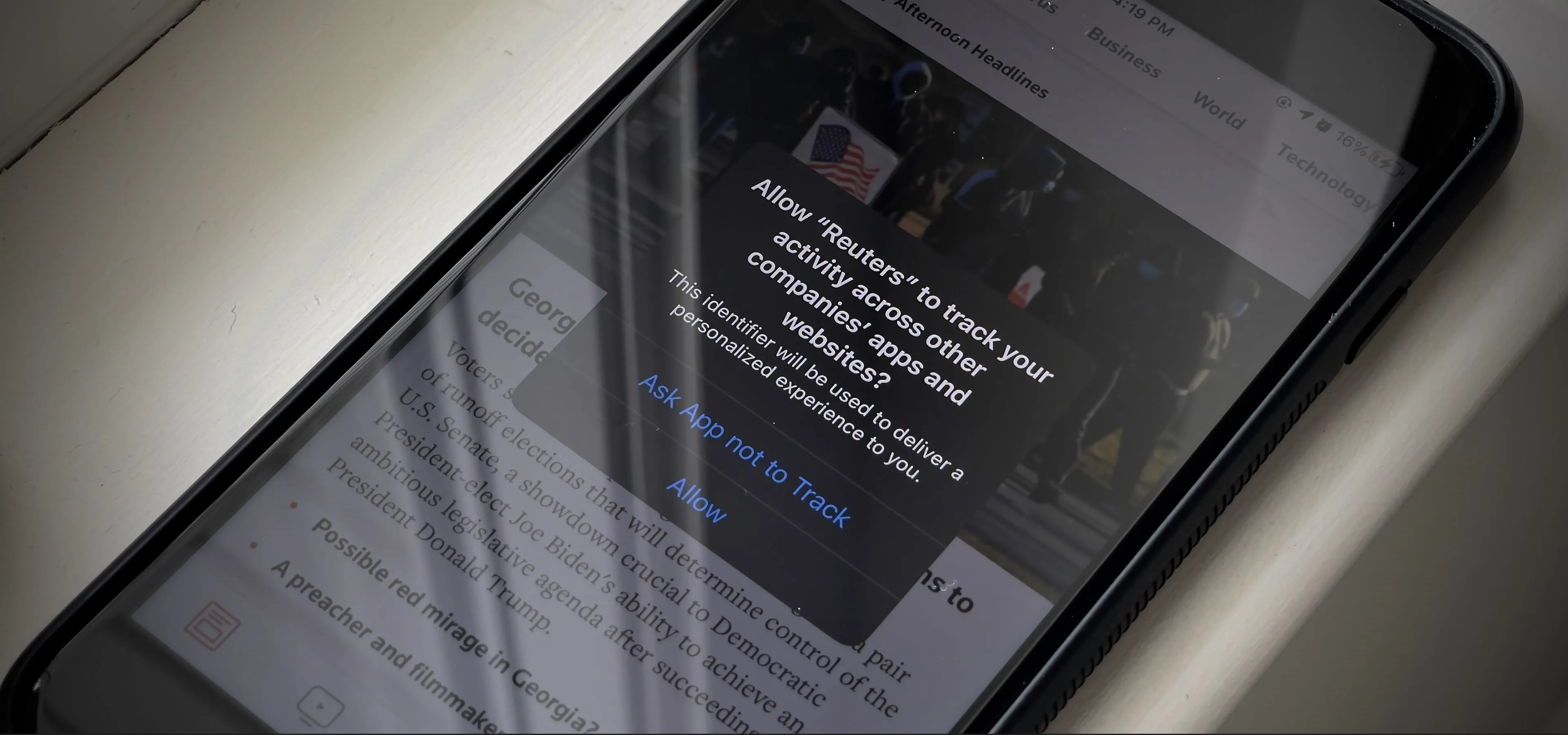
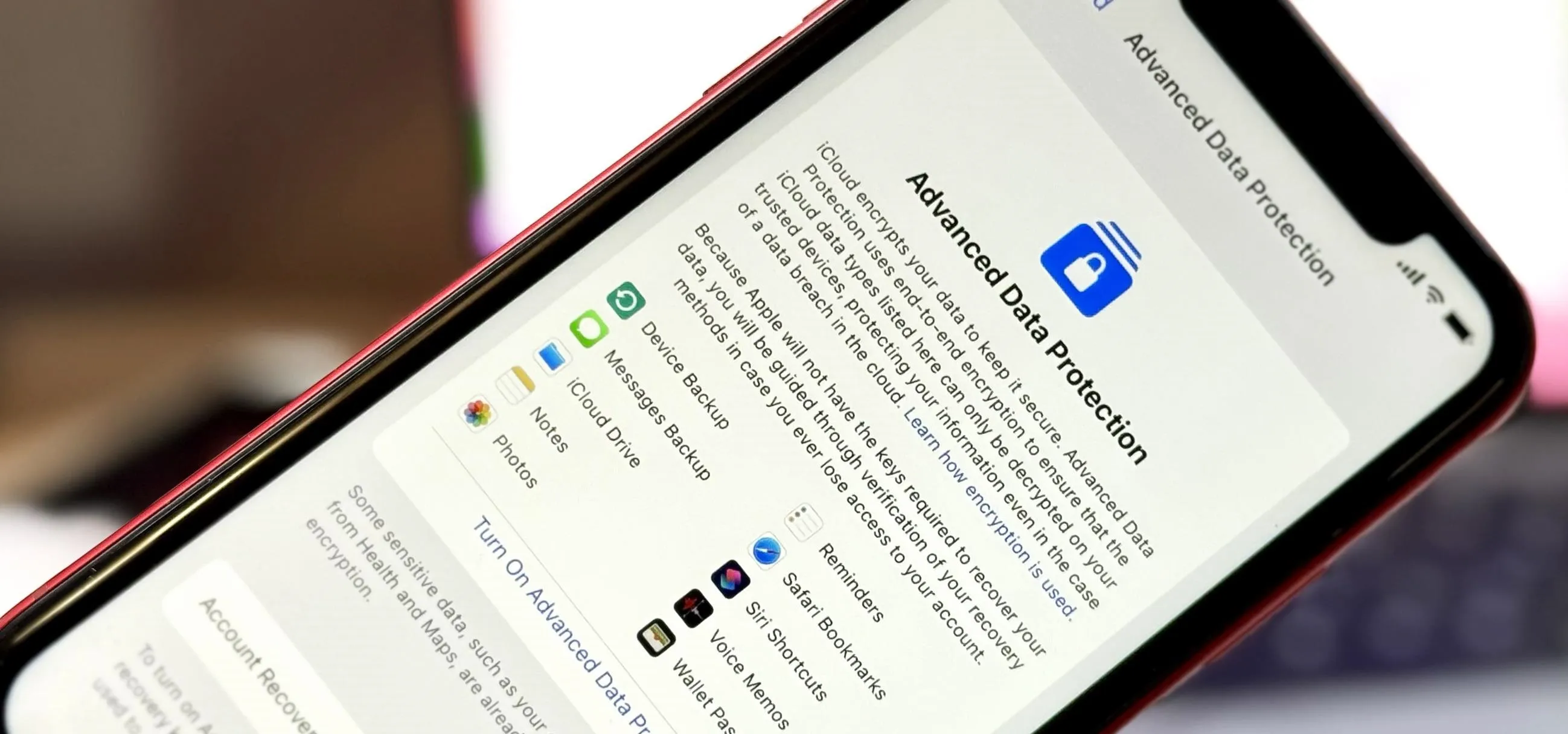
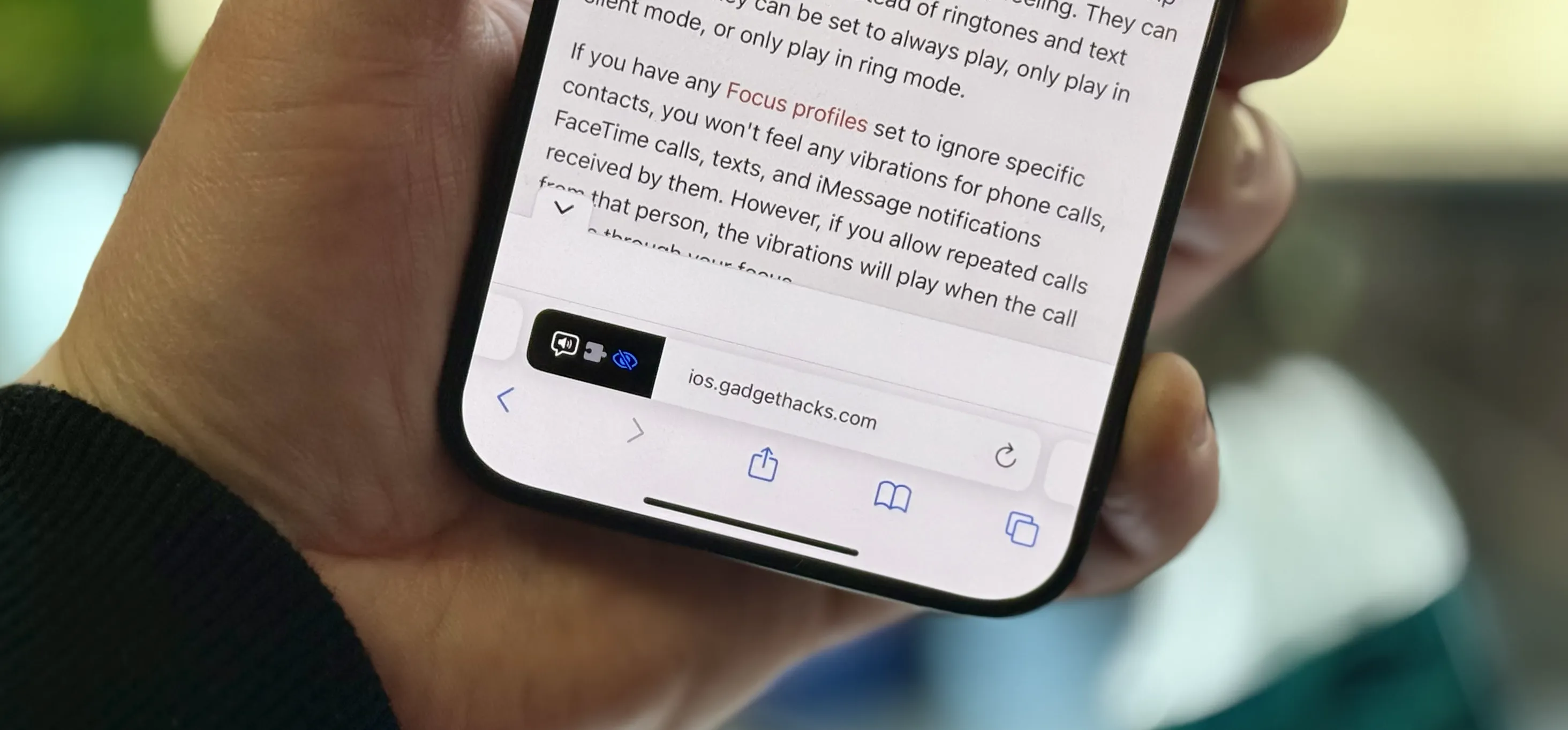
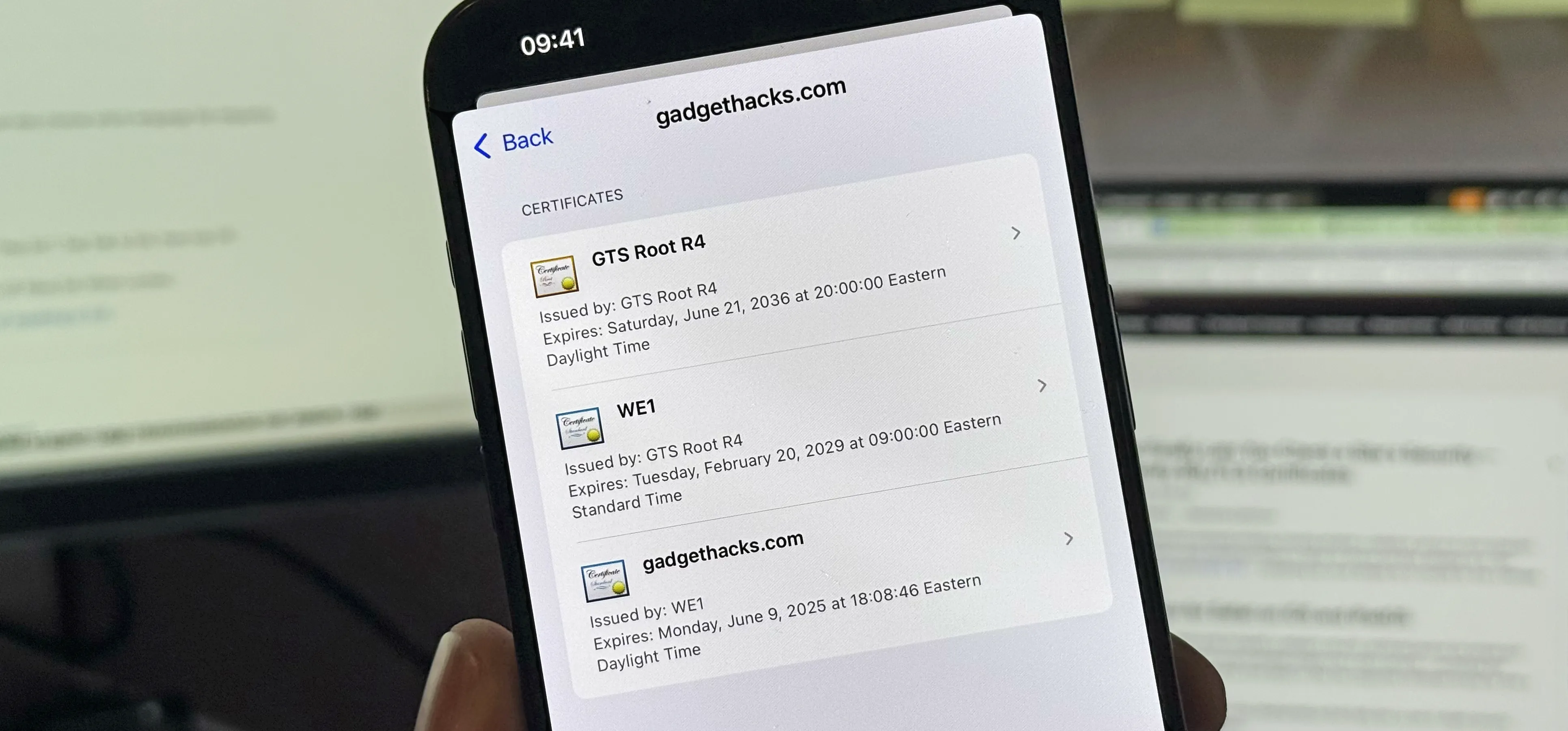
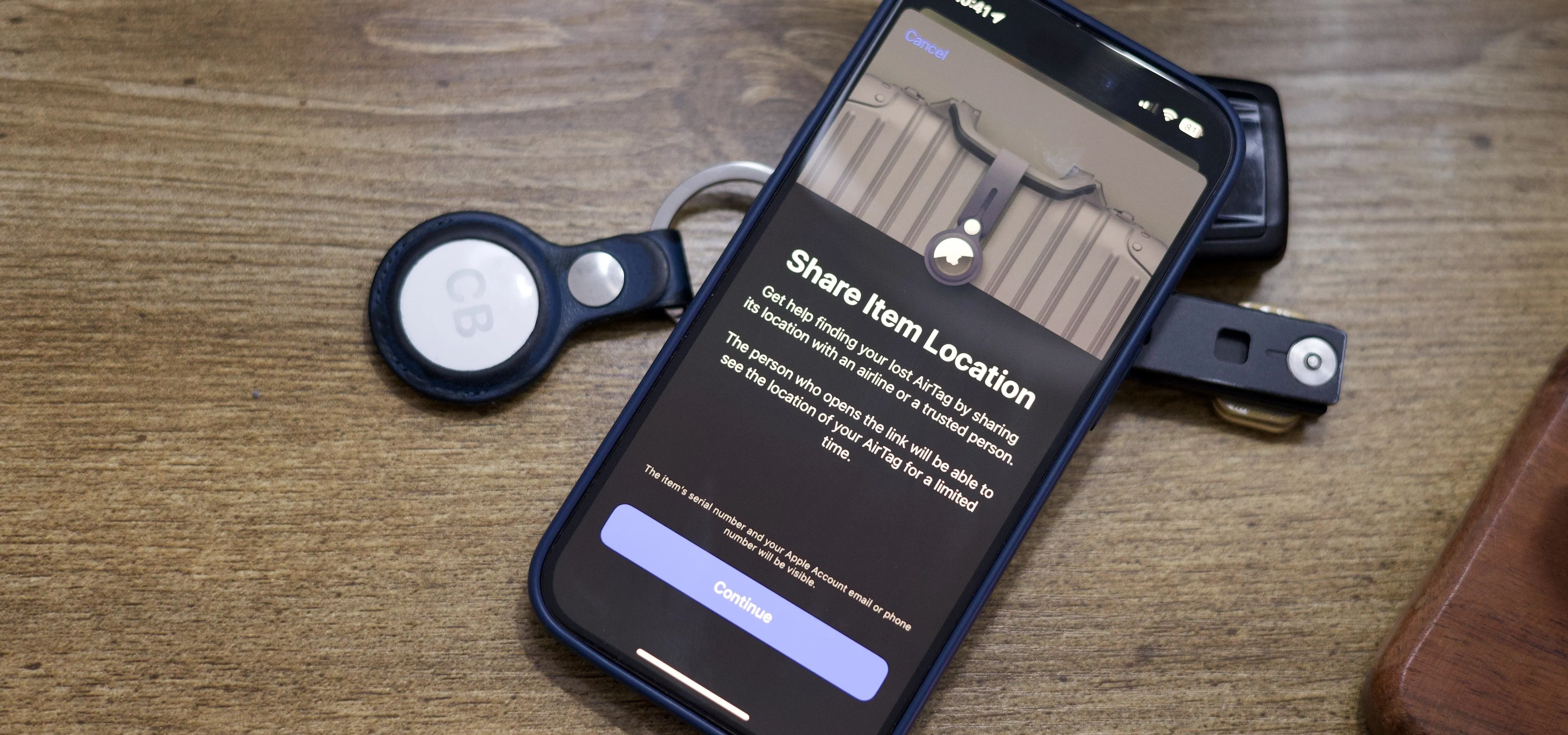
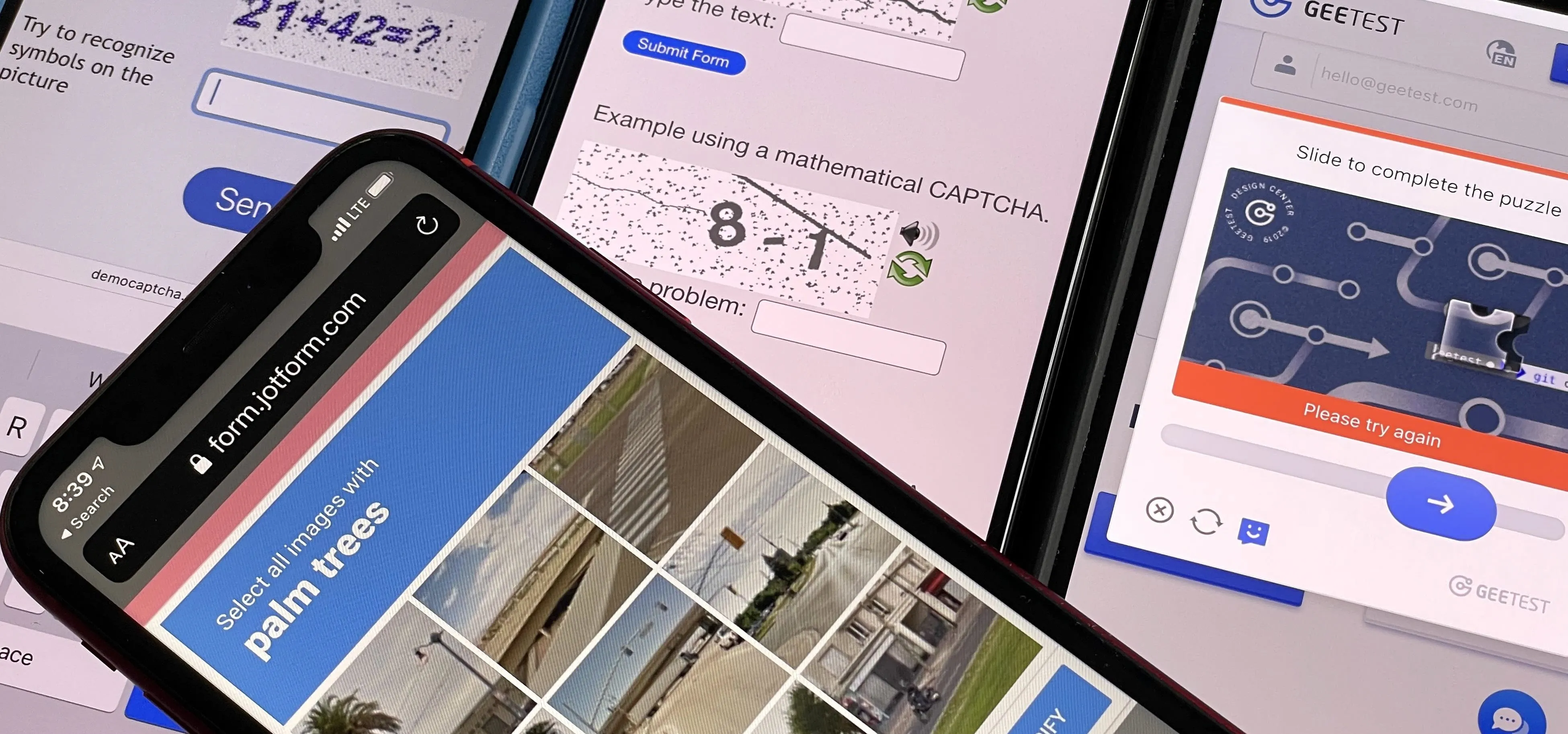
iOS Security

how to
The Most Important Photos App Feature You Should Be Using on Your iPhone or iPad

how to
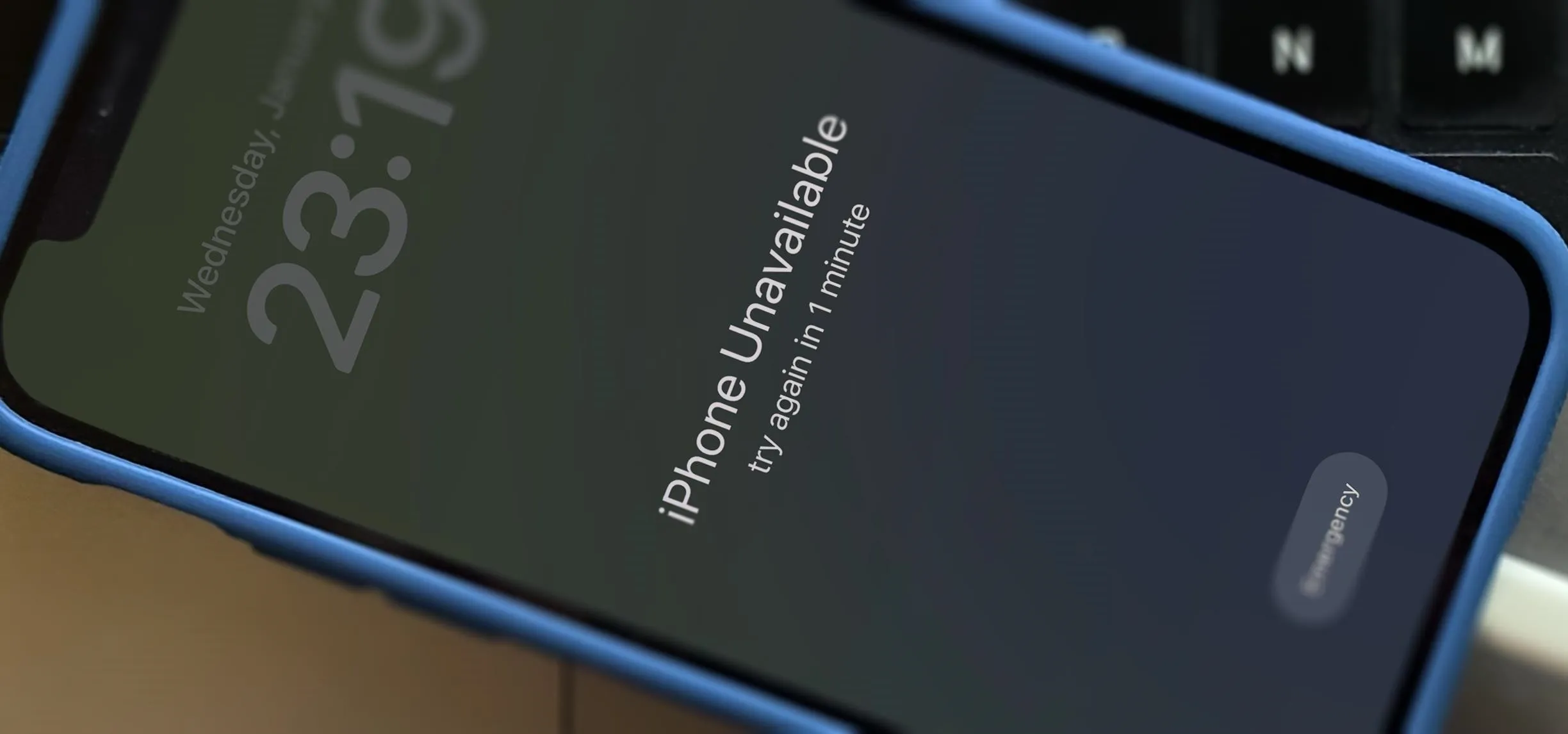
How to Lock and Hide Apps on Your iPhone or iPad — The Official Way


how to
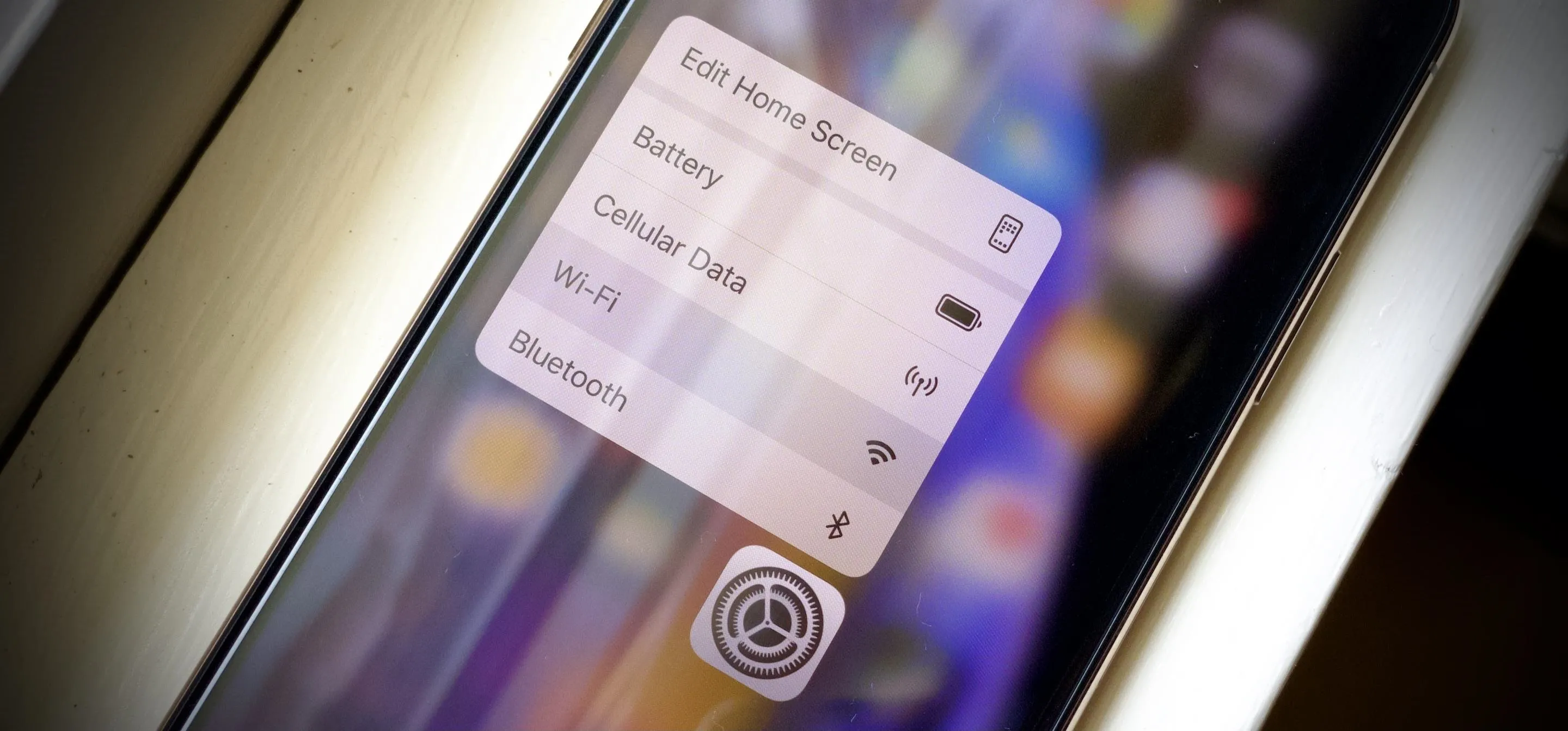
The Easiest Way to Find, Share, and Manage Wi-Fi Passwords Your iPhone and Other Apple Devices Auto-Saved for You
Featured On Gadget Hacks:
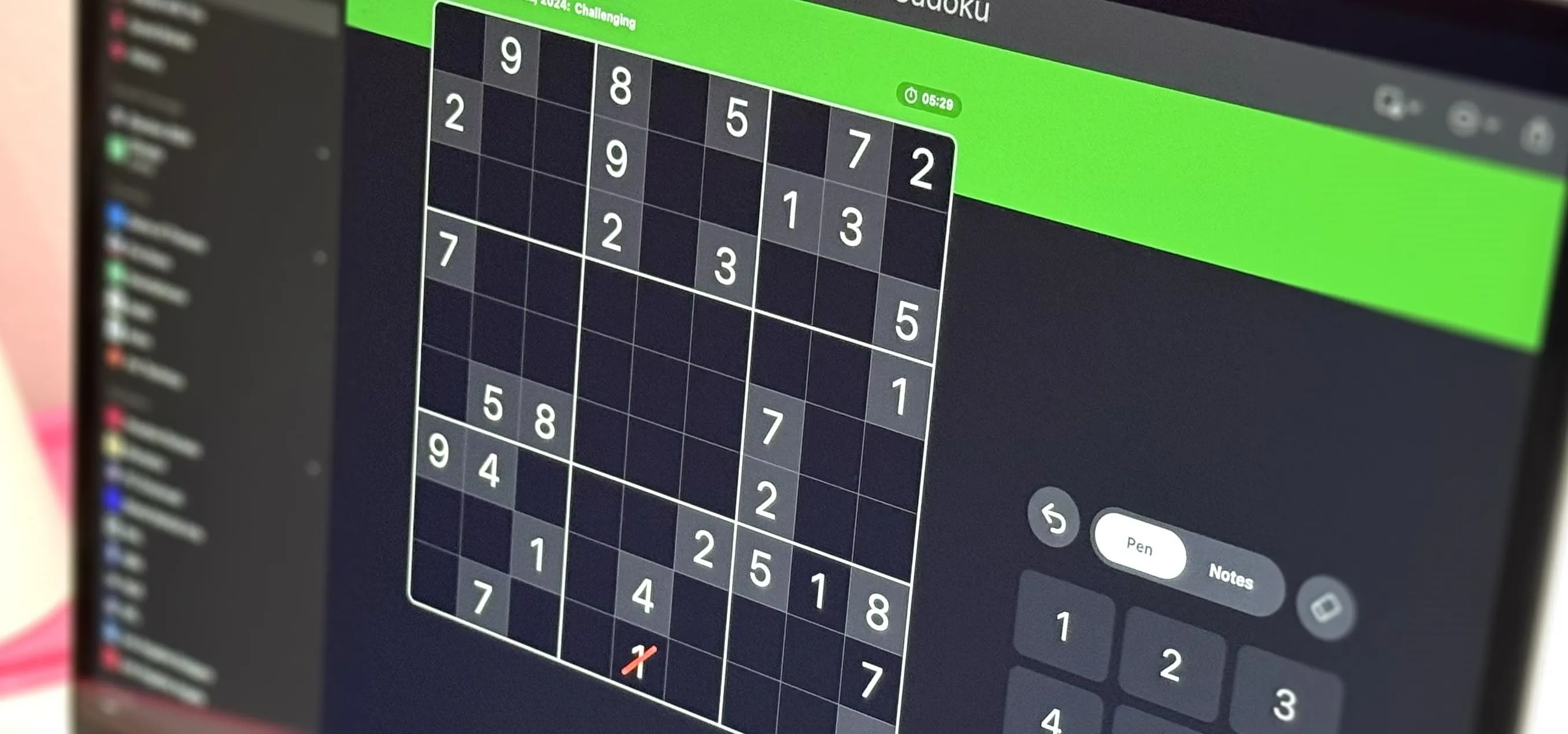
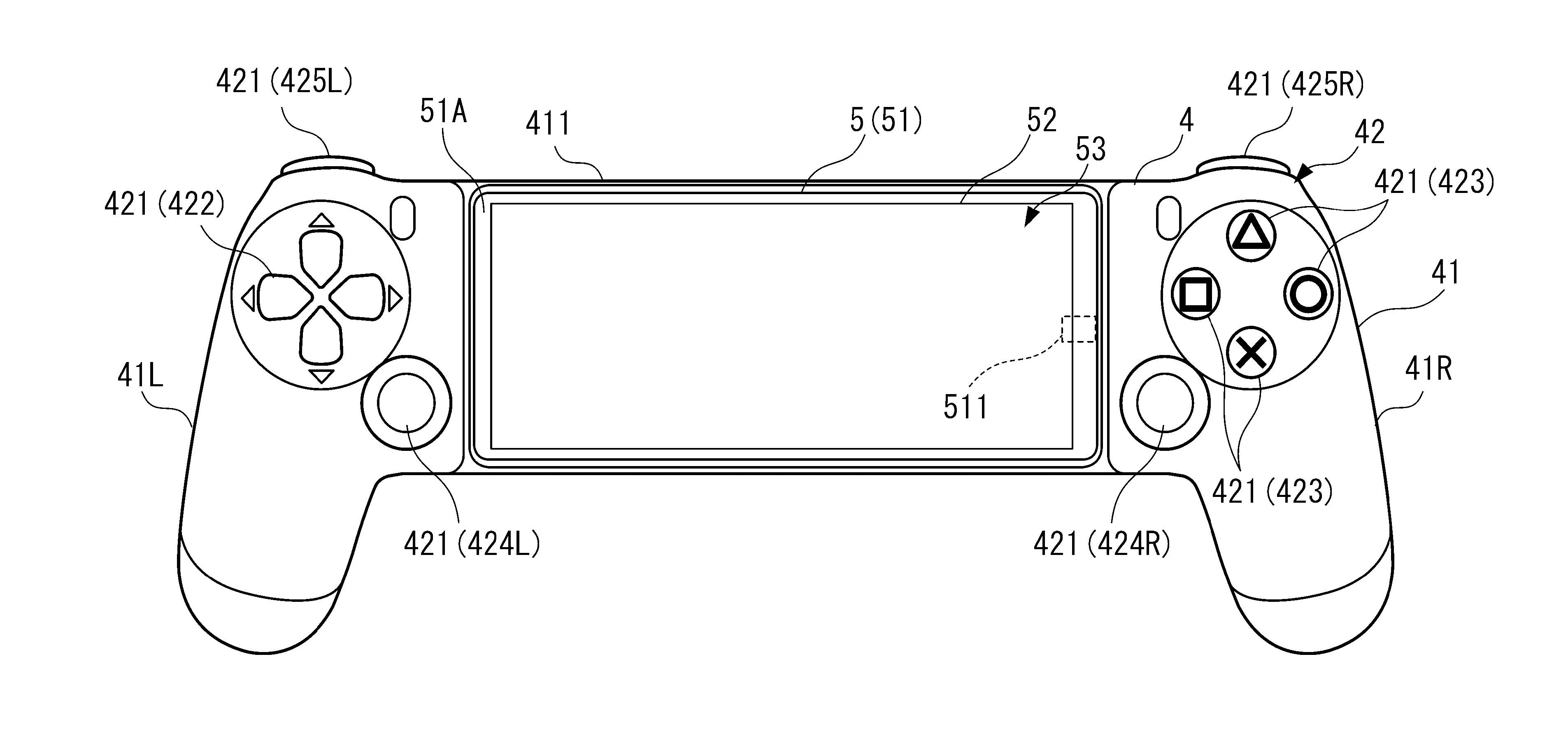
Gaming









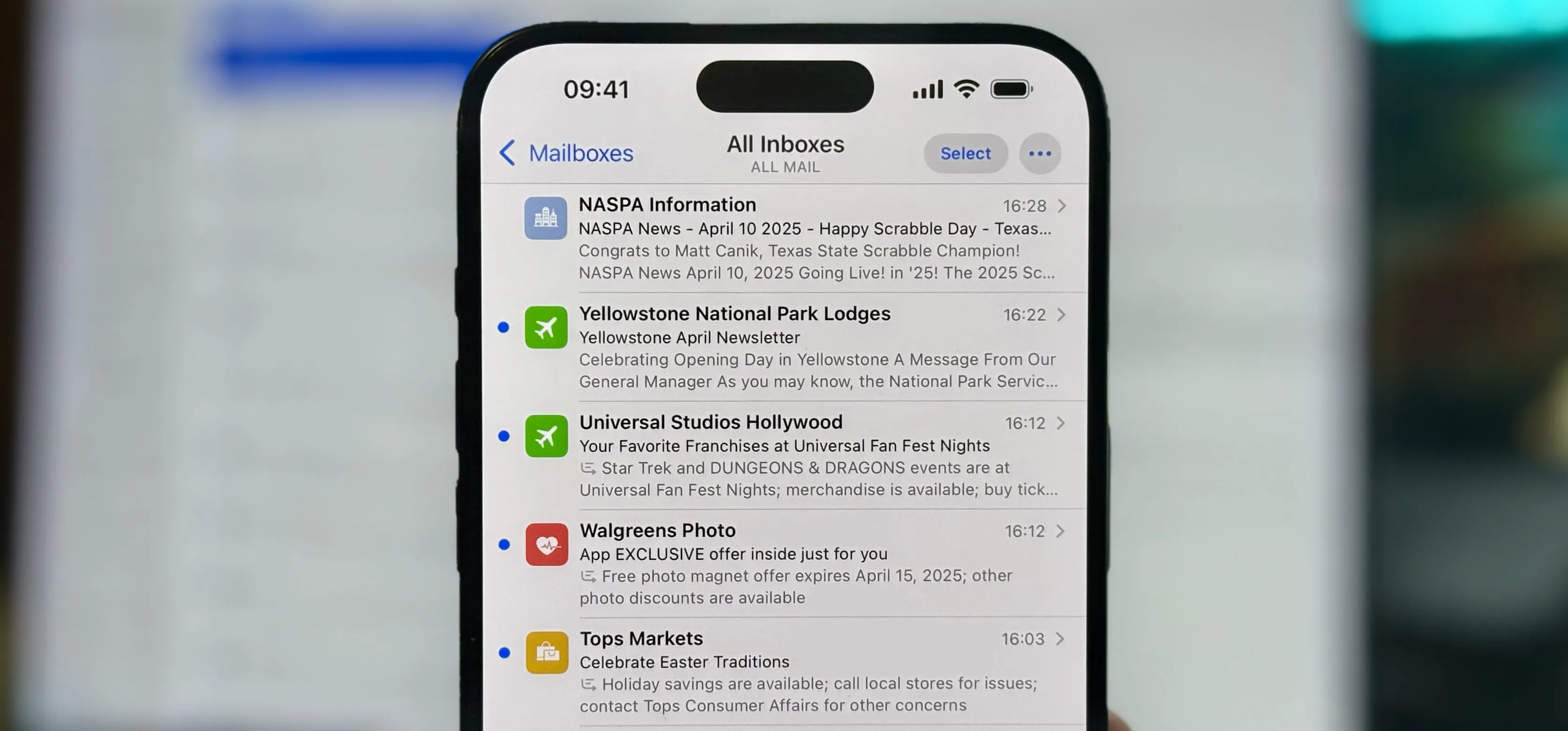
Featured On Gadget Hacks:
iOS 18









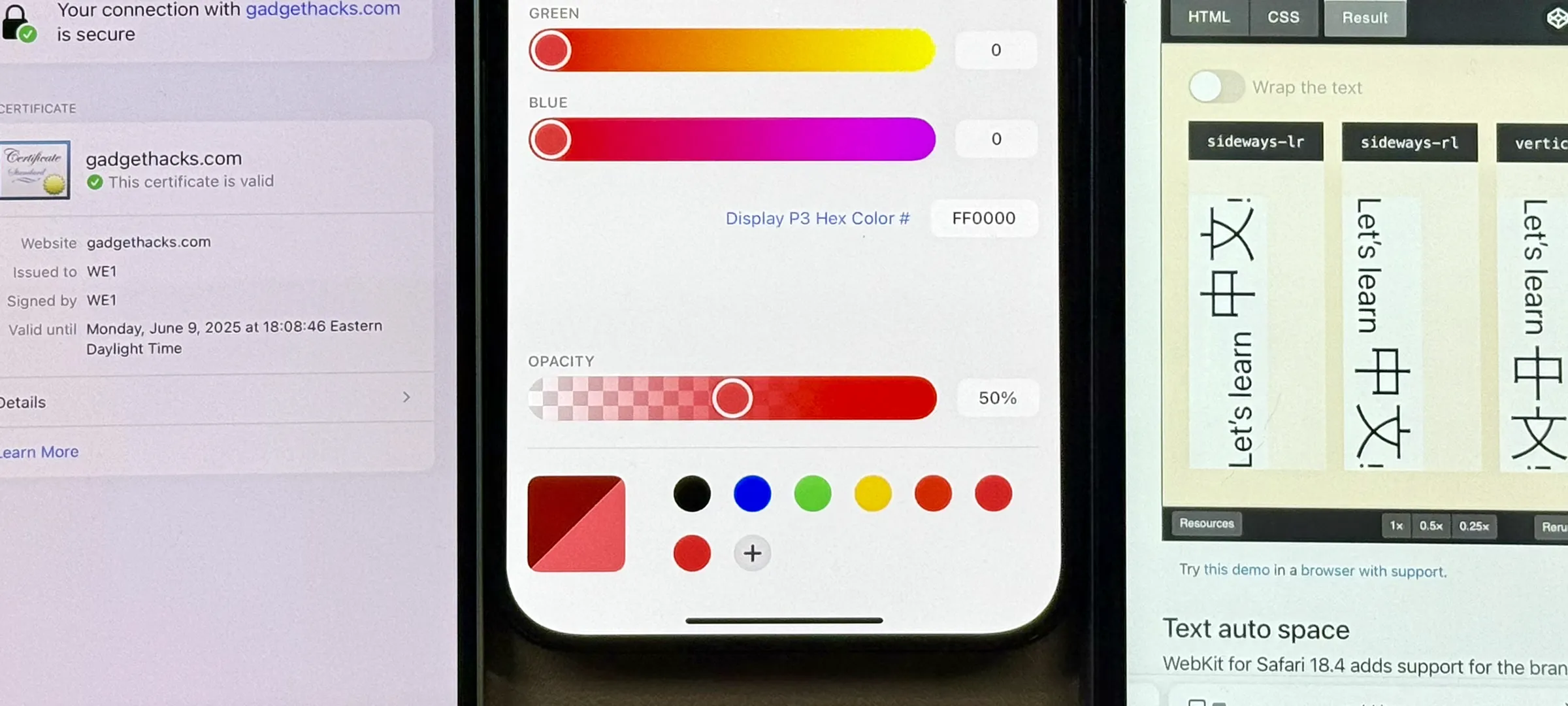
Featured On Gadget Hacks:
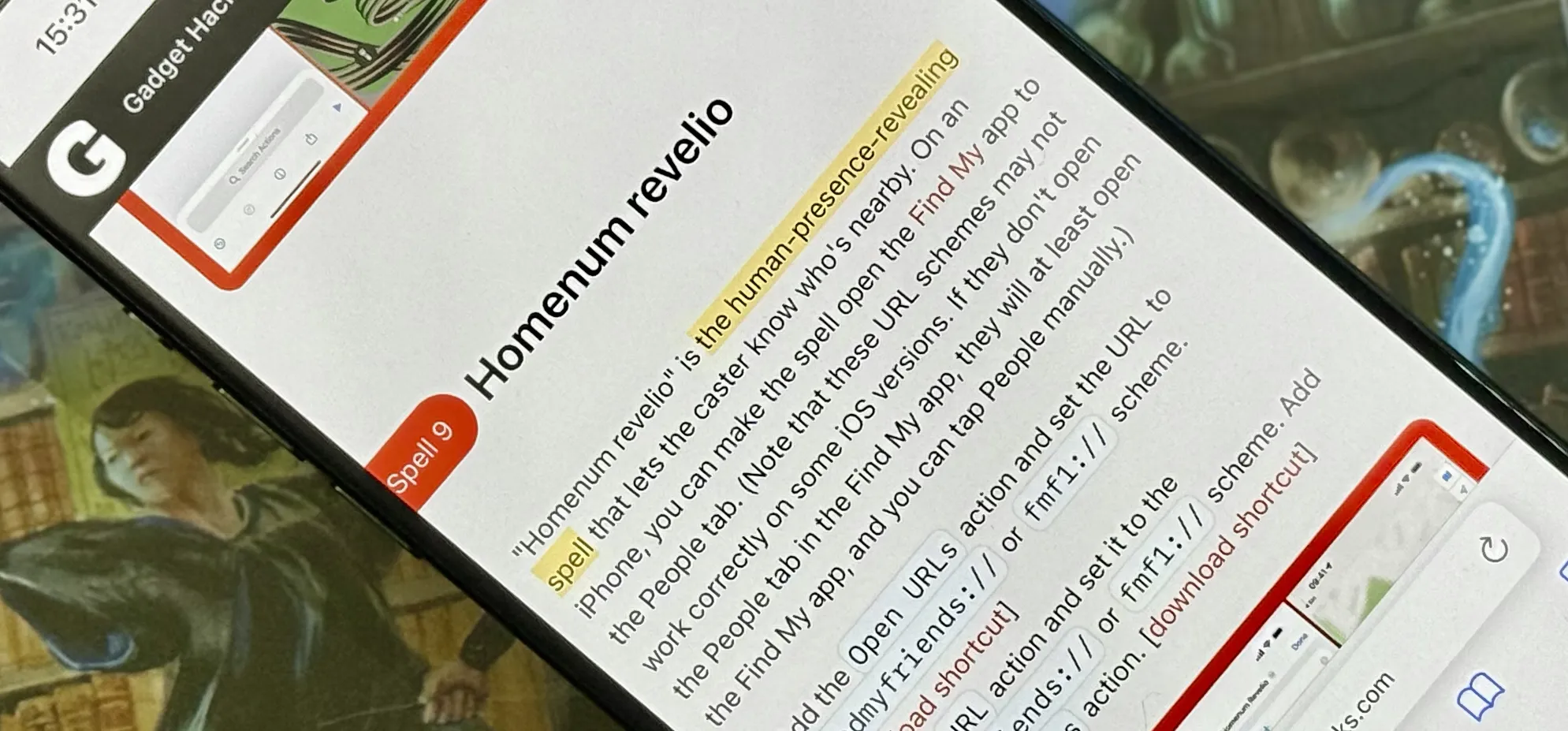
Productivity & Shortcuts






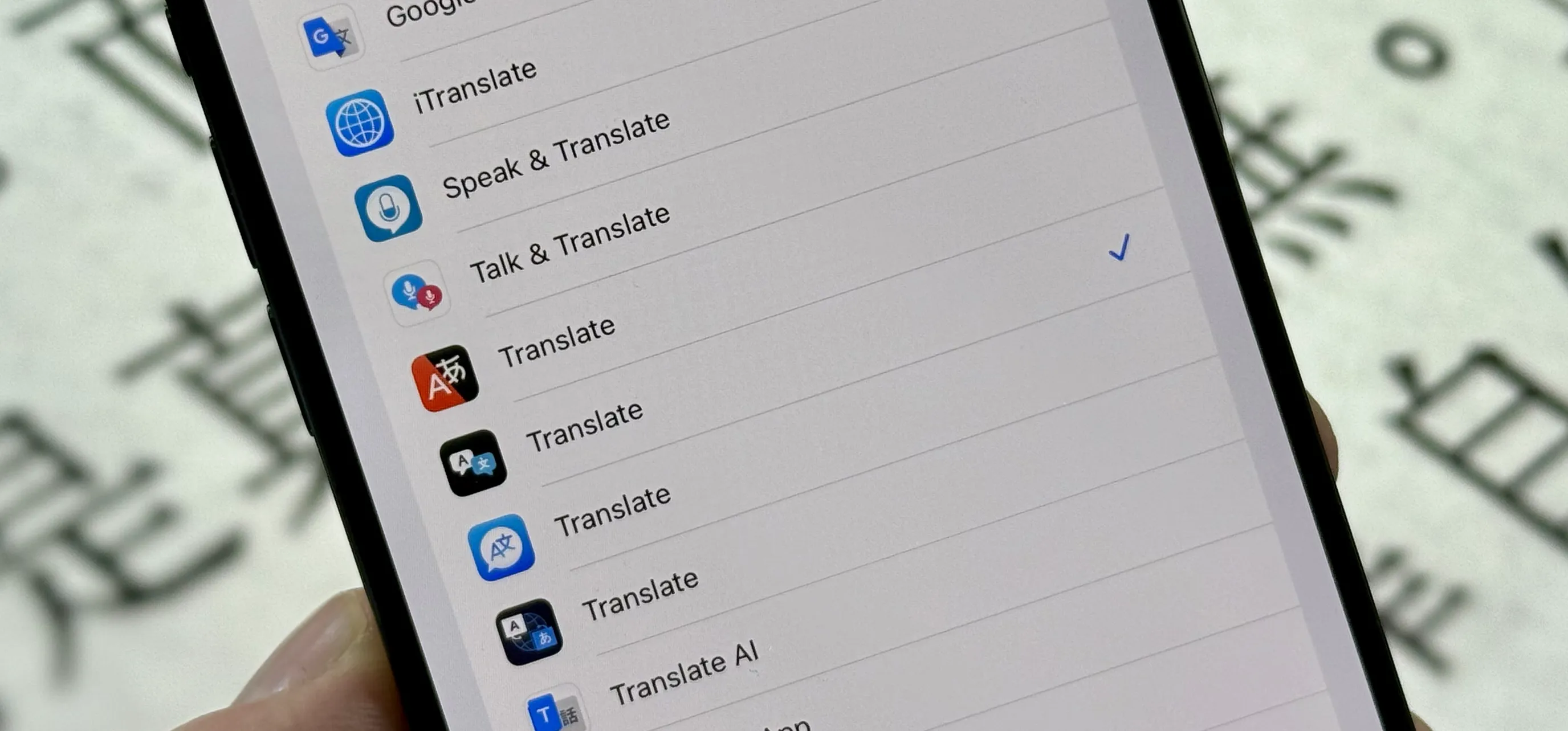
Featured On Gadget Hacks:
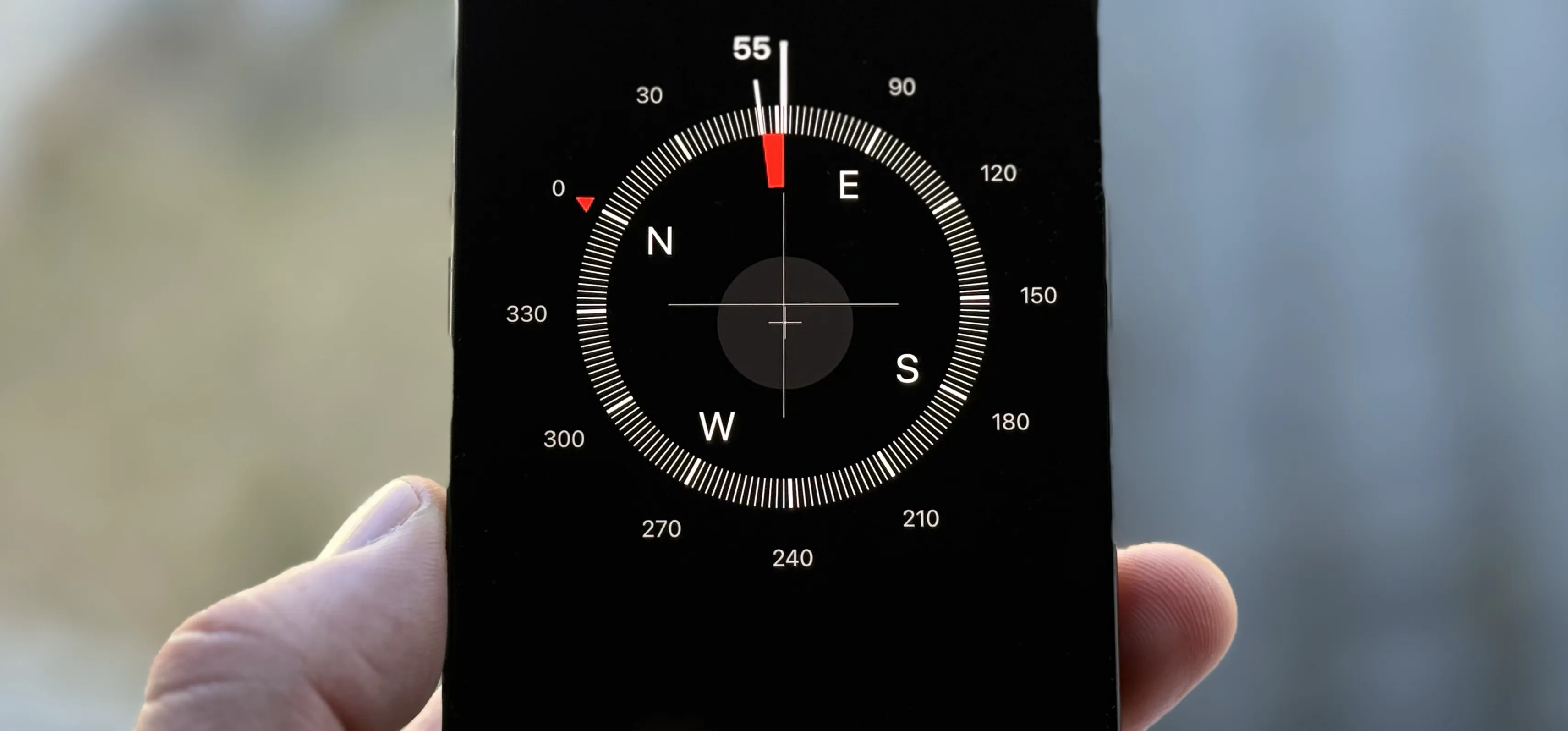
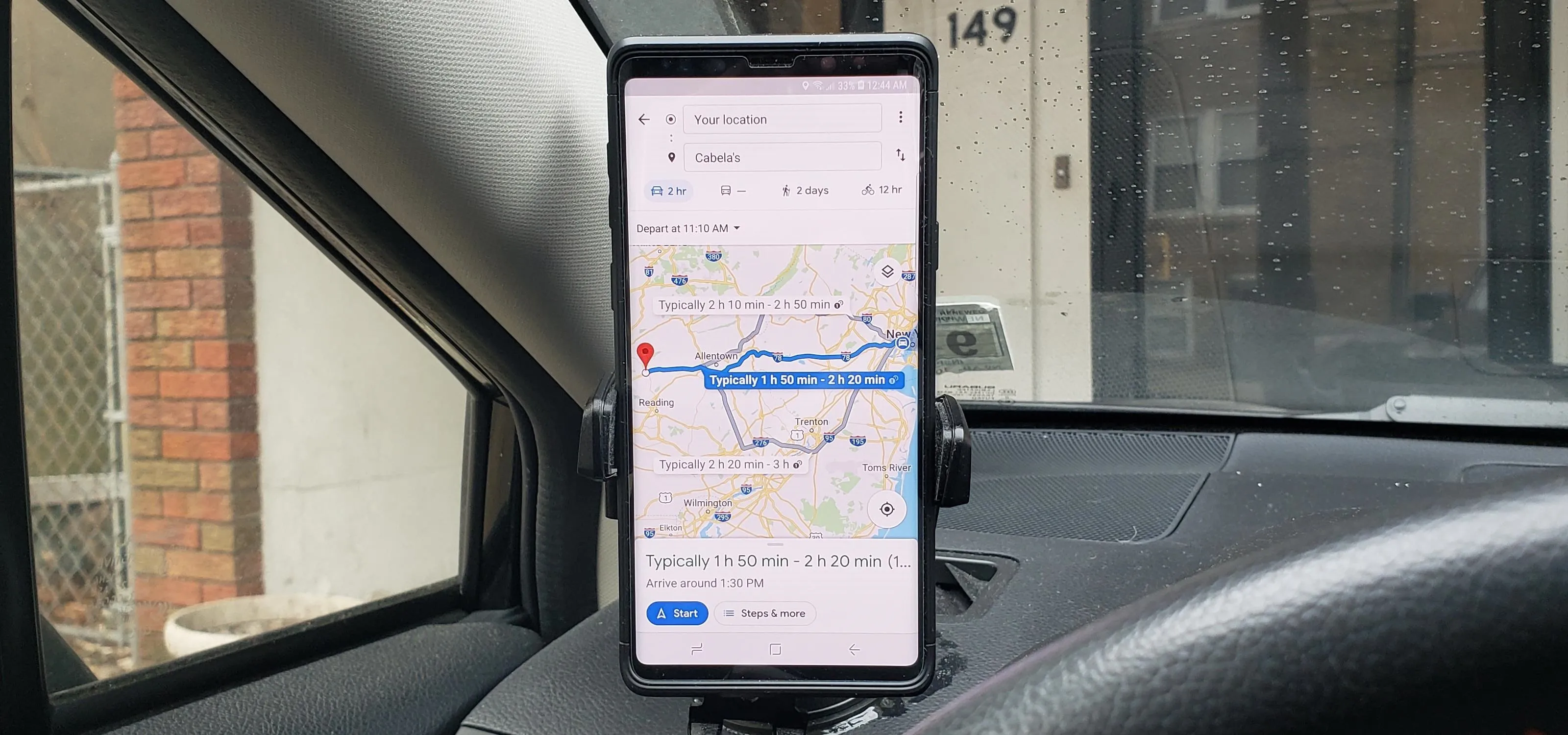
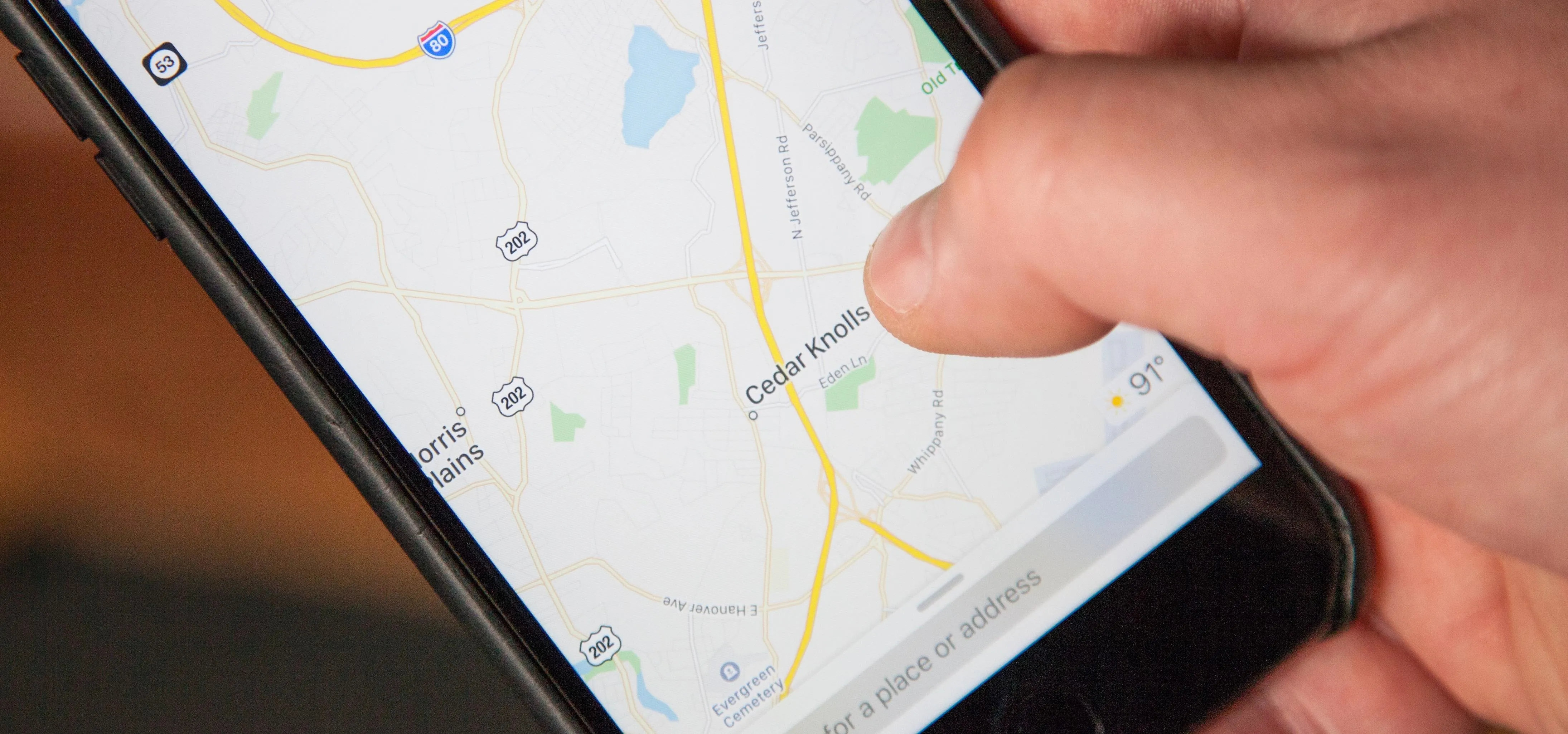
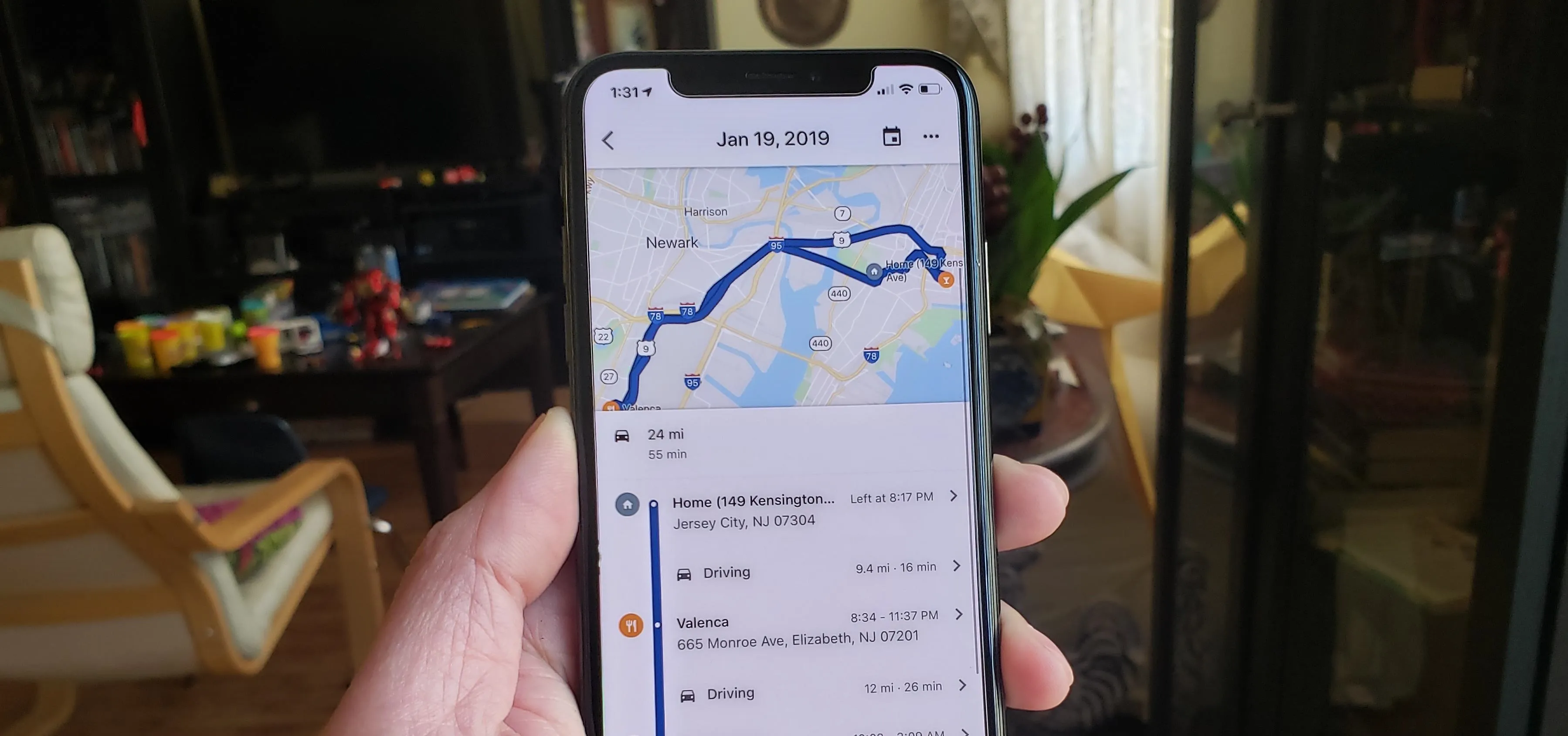
Travel Tips for Your Phone