When it comes to security, Apple is usually at the top of the pack when it comes to your personal data, minus a few embarrassing flaws here and there. However, a new iOS security concern has been discovered that protects your data less than it did before — and Apple designed it like that.
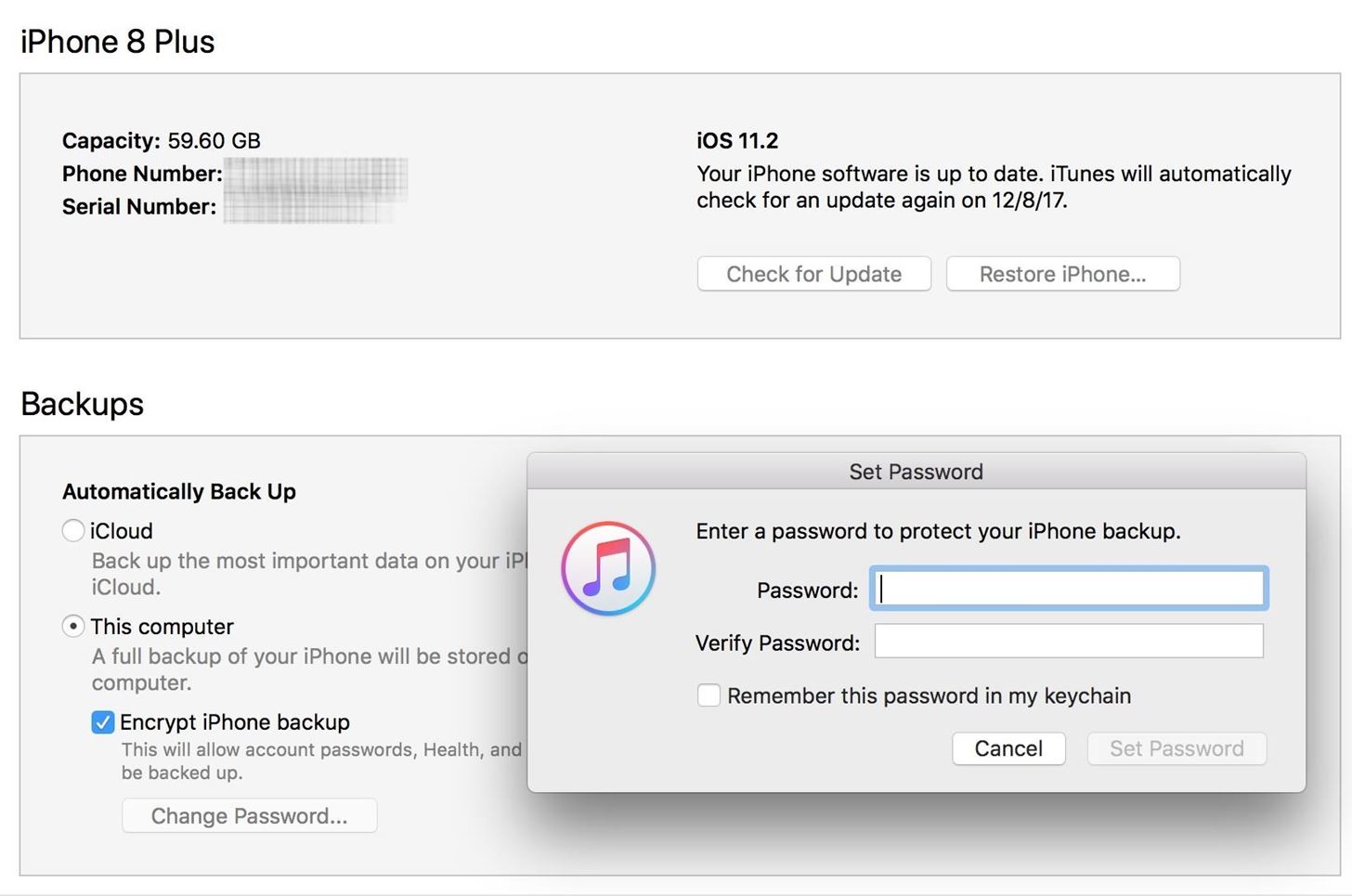
The issue concerns your encrypted iOS backups in iTunes for, say, your iPhone. These backups, unlike unencrypted backups, include information such as your saved passwords, Wi-Fi settings, website history, and health data. If you'd like to retain all this data should you need to restore your iPhone, an encrypted backup is great, but needs to be set up. By default, iOS backups in iTunes are not encrypted.
Encrypted Backups, Then & Now
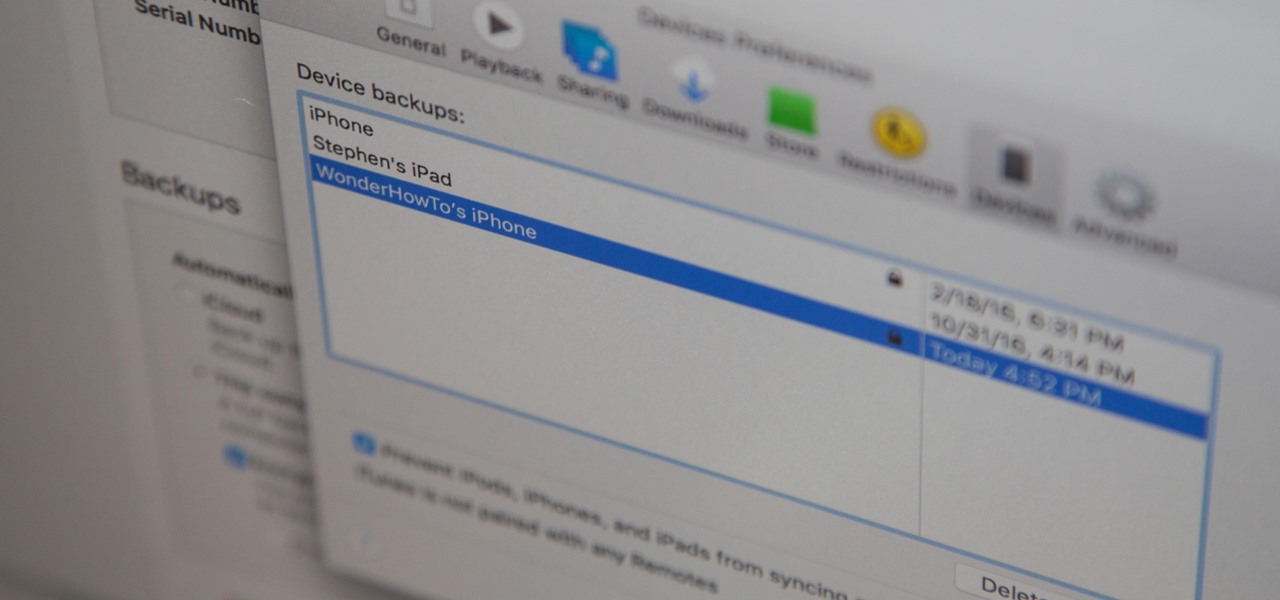
When first setting up encrypted backups in iTunes, you create a password specifically for the backup which protects all your data. If you should ever backup your iPhone onto another computer, it would retain the same password — no matter how many times you backed up your iPhone or switched computers. Before Apple's change in security tactics, if you forgot the password, you had no way to get it back, and you'd be forced to factory reset your iPhone.
With iOS 11, Apple flipped the rules. Now, you can update your password if you forget it using your iPhone's passcode. While certainly convenient for iPhone users — a four- to six-digit passcode is easier to remember than a full password — the concern here is the ease with which an attacker could compromise your data. That easy-to-remember passcode is potentially an easy-to-guess key to your iPhone.
You can't restore an encrypted backup without its password. With iOS 11 or later, you can make a new encrypted backup of your device by resetting the password. Here's what to do:
- On your iOS device, go to Settings > General > Reset.
- Tap Reset All Settings and enter your iOS passcode.
- Follow the steps to reset your settings. This won't affect your user data or passwords, but it will reset settings like display brightness, Home screen layout, and wallpaper. It also removes your encrypted backup password.
- Connect your device to iTunes again and create a new encrypted backup.
You won't be able to use previous encrypted backups, but you can back up your current data using iTunes and setting a new backup password.
However, the concern may be a bit overblown. To accomplish this task, an intruder would not only need to know your passcode or be able to crack it (there are brute-force tools that can do this), but would also need physical access to your iPhone. And while they won't be able to use the encrypted backup you already had, they can create a new one and use tools to access the data within, including account passwords, photos, and more.
Perhaps worse than this encrypted backups issue is that Apple also lets you reset your Apple ID with two-factor authentication. So, if someone does have your iPhone and was able to crack the passcode, they could go online and change your Apple ID password so they can turn off the iCloud lock on your iPhone and reactivate the device on another account, among other things.
So, sounds like you're pretty much screwed, right? Only if you don't care about protecting your iPhone with a good, strong passcode that hackers and thieves will have an impossible time guessing or brute-forcing.
How to Really Protect Your Encrypted Backups
The real focus here should be on the importance of using a strong passcode with your iPhone. While a six-digit passcode offers one-million possible entries, you can do better — an alphanumeric passcode ensures a hacker with access to your iPhone has their work cut out for them.
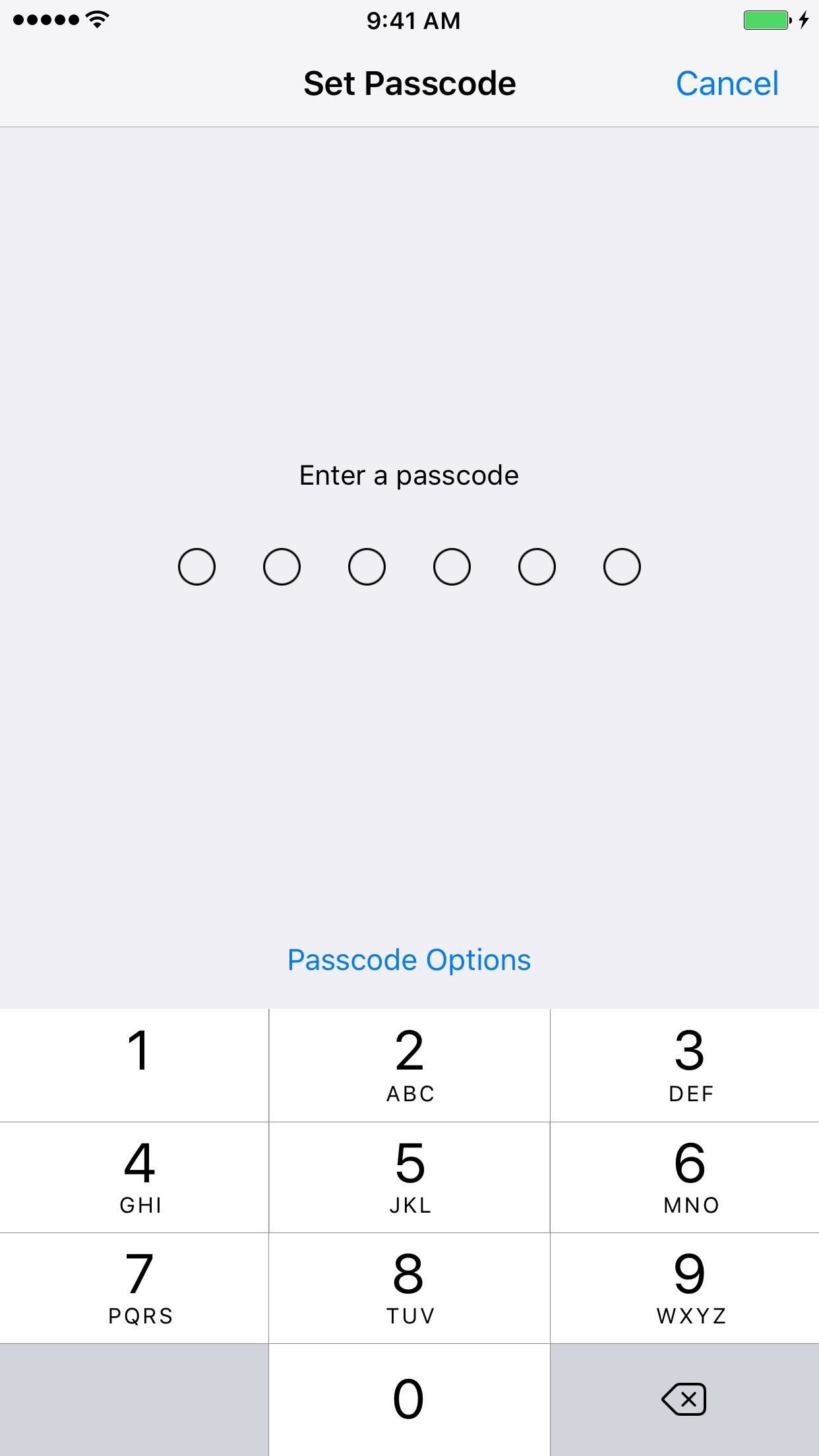
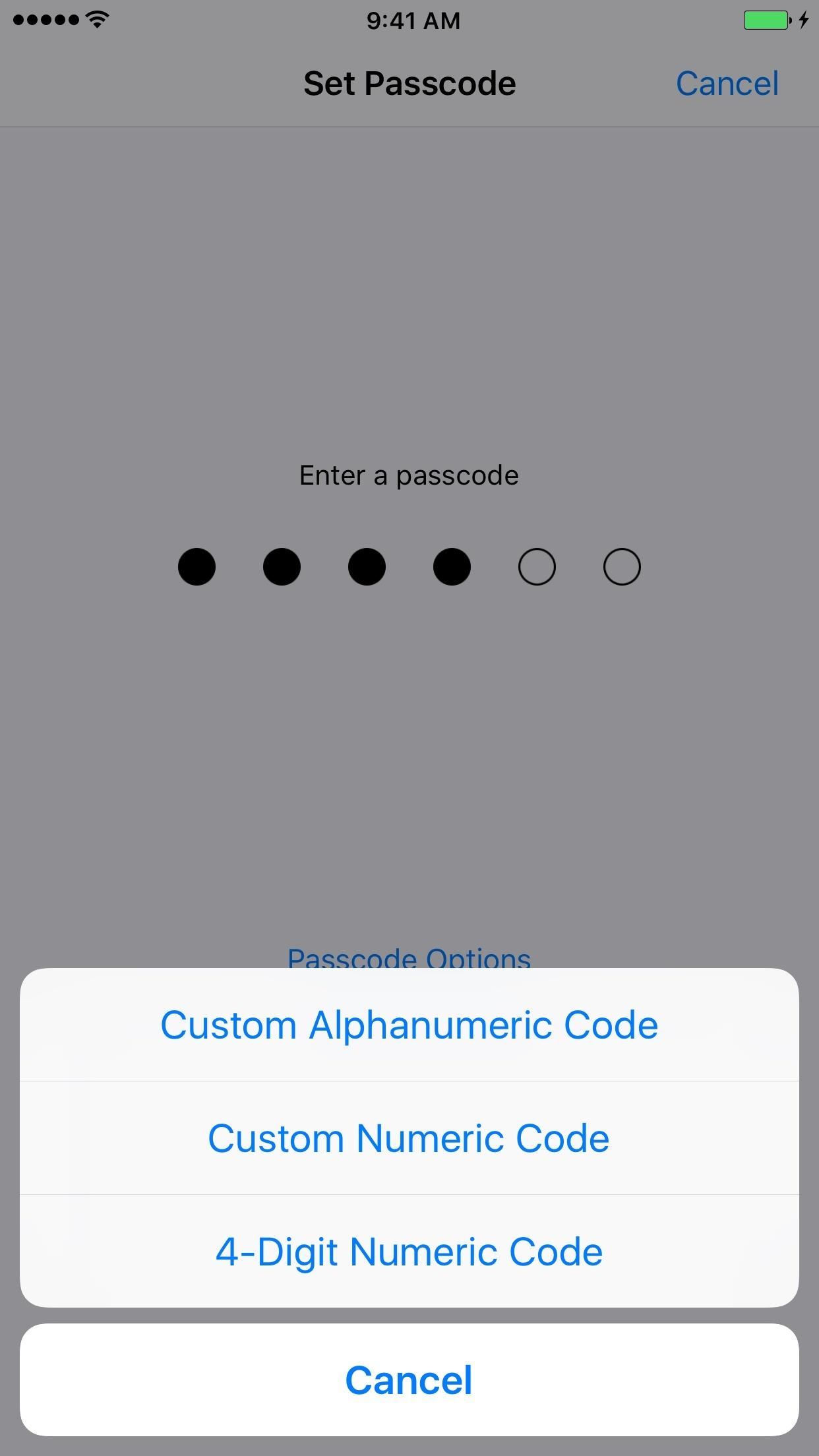
A good passcode will protect you from most security concerns. Yes, there are vulnerabilities (no passcode is 100% perfect), but at the end of the day, a passcode with the right specifications should give you some peace of mind. After all, resetting your encrypted backup password requires knowing your passcode. The stronger you make it, the safer your backup and all the data within will be.
For more information on making a strong alphanumeric passcode for your iPhone, Null Byte has a great guide on password-making tips from a hacker's perspective.
If you own an iPhone X with Face ID or another model iPhone with Touch ID, you may be wondering how that all plays into this. Well, biometric authentication doesn't. If someone forces you to use your face or fingerprint to unlock the device, they'd still need the passcode to work with encrypted backups. Still, if you're worried, you can quickly disable Face ID and Touch ID in mere seconds.
And if you're using Face ID or Touch ID, then that's even a better reason to make sure you get a strong passcode. Since you won't be required to input the passcode onto your iPhone all of the time, you won't have to enter your new complicated alphanumeric passcode unless you restart, disable biometrics as mentioned above, it hasn't been unlocked for over 48 hours, after unsuccessful attempts to recognize your face or fingerprint, and a few other scenarios.
Just updated your iPhone? You'll find new features for Podcasts, News, Books, and TV, as well as important security improvements and fresh wallpapers. Find out what's new and changed on your iPhone with the iOS 17.5 update.





















Be the First to Comment
Share Your Thoughts