You would think that with each major iOS update, there'd be fewer ways to bypass the lock screen. Unfortunately, Apple's developers have consistently failed every year since 2013 in this department, leaving open lock screen exploits for iOS 7, iOS 8, and now the latest iOS version, iOS 9, with each exploit being discovered within days of the OS release.
The latest exploit, which can be seen in the video below from YouTube user videosdebarraquito, is reported to work from iOS 8.4 to 9.0.1. While it may not grant full access to your iPad or iPhone, it does permit anyone to view your contacts and photos without a passcode, which is where some of your more sensitive content might reside.
How the Exploit Works
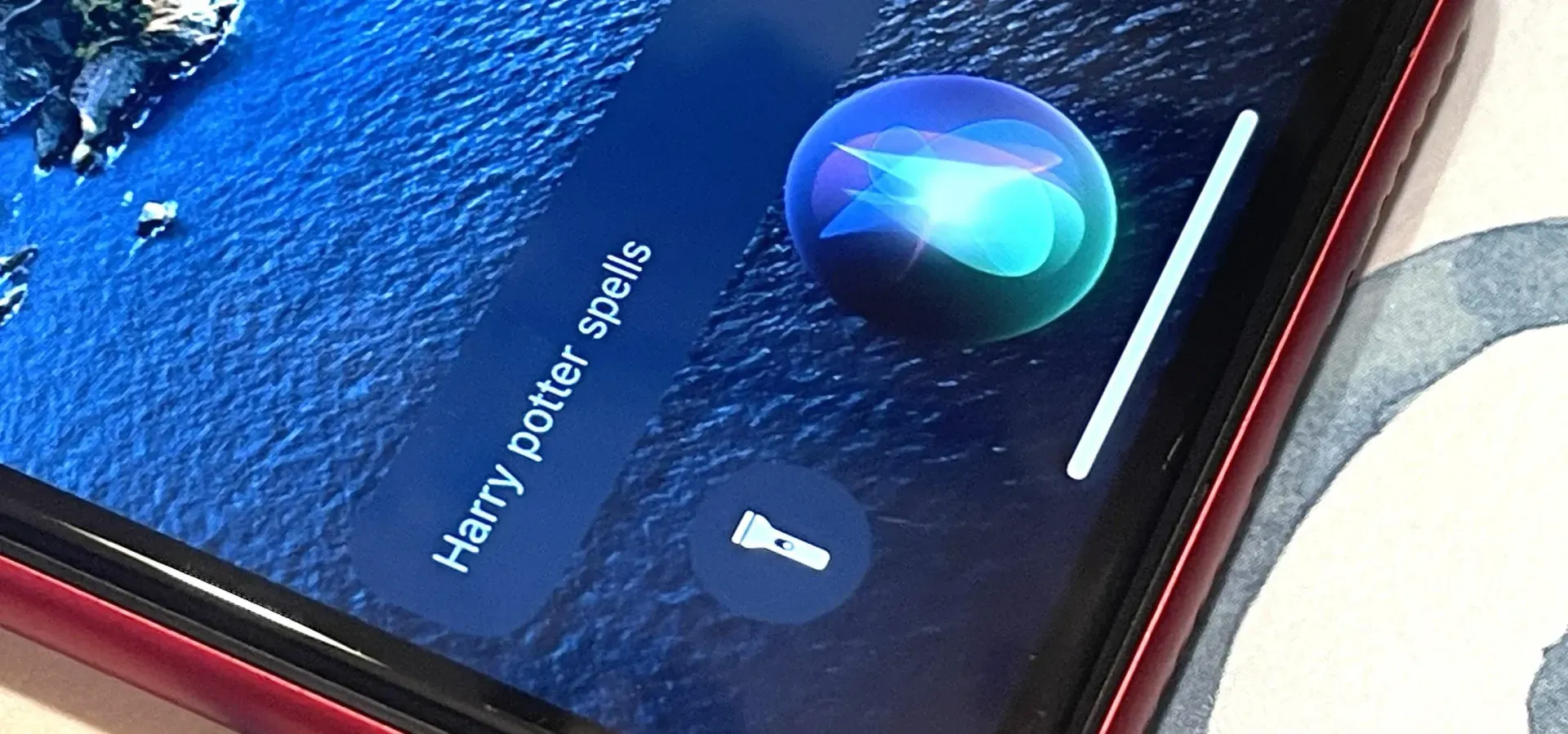
You have to enter an incorrect passcode four times, then on the fourth attempt, enter three digits, then hold down the Home button to activate Siri while you enter the fourth digit in. From there, you're able to access contacts and add a profile picture, which grants access to the Photos app where all your pictures are. You can see the whole exploit in action below.
How to Protect Yourself
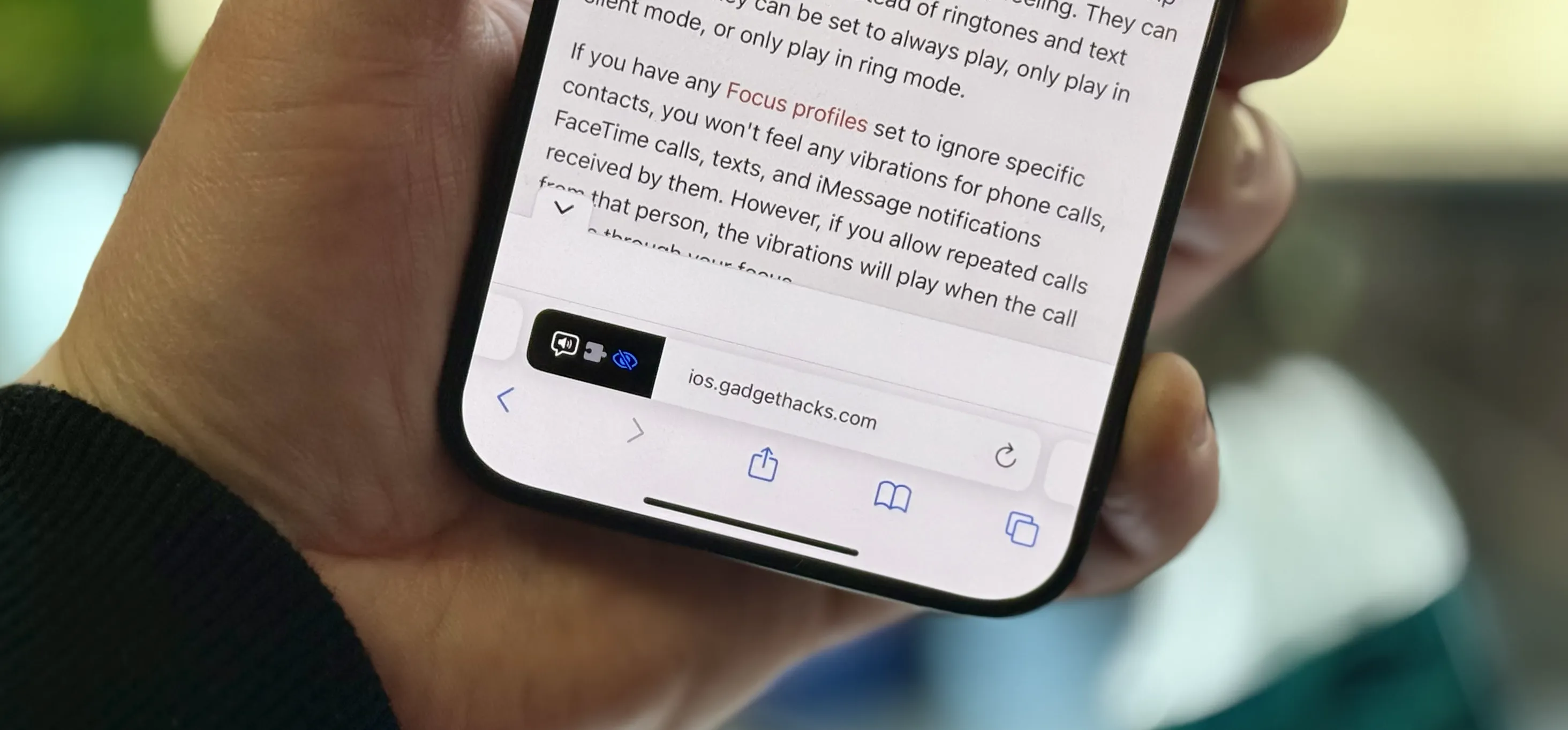
Since the exploit utilizes Siri, all you need to do is disable her on the lock screen. To do this, navigate to Settings -> Touch ID & Passcode, then toggle off Siri under the section labeled "Allow Access When Locked." With Siri off and unable to serve as an accomplice in the exploit, you'll be safe... until the next security flaw anyway.

Follow Apple Hacks over on Facebook and Twitter, or Gadget Hacks over on Facebook, Google+, and Twitter, for more Apple tips.














Comments
Be the first, drop a comment!