If you've haven't had your fill of Apple's security issues in recent weeks, Siri is now the latest to join the slew of problems with the most recent version of iOS (7.1.1).
The newest bug, discovered by Sherif Hashim, allows anyone to easily bypass passcode security measures (unless you have Touch ID enabled) to access the device's contact list, where they can then pull phone numbers to either call, email, or message. All of this is done with just a few voice commands to Siri.
How It's Intended to Work
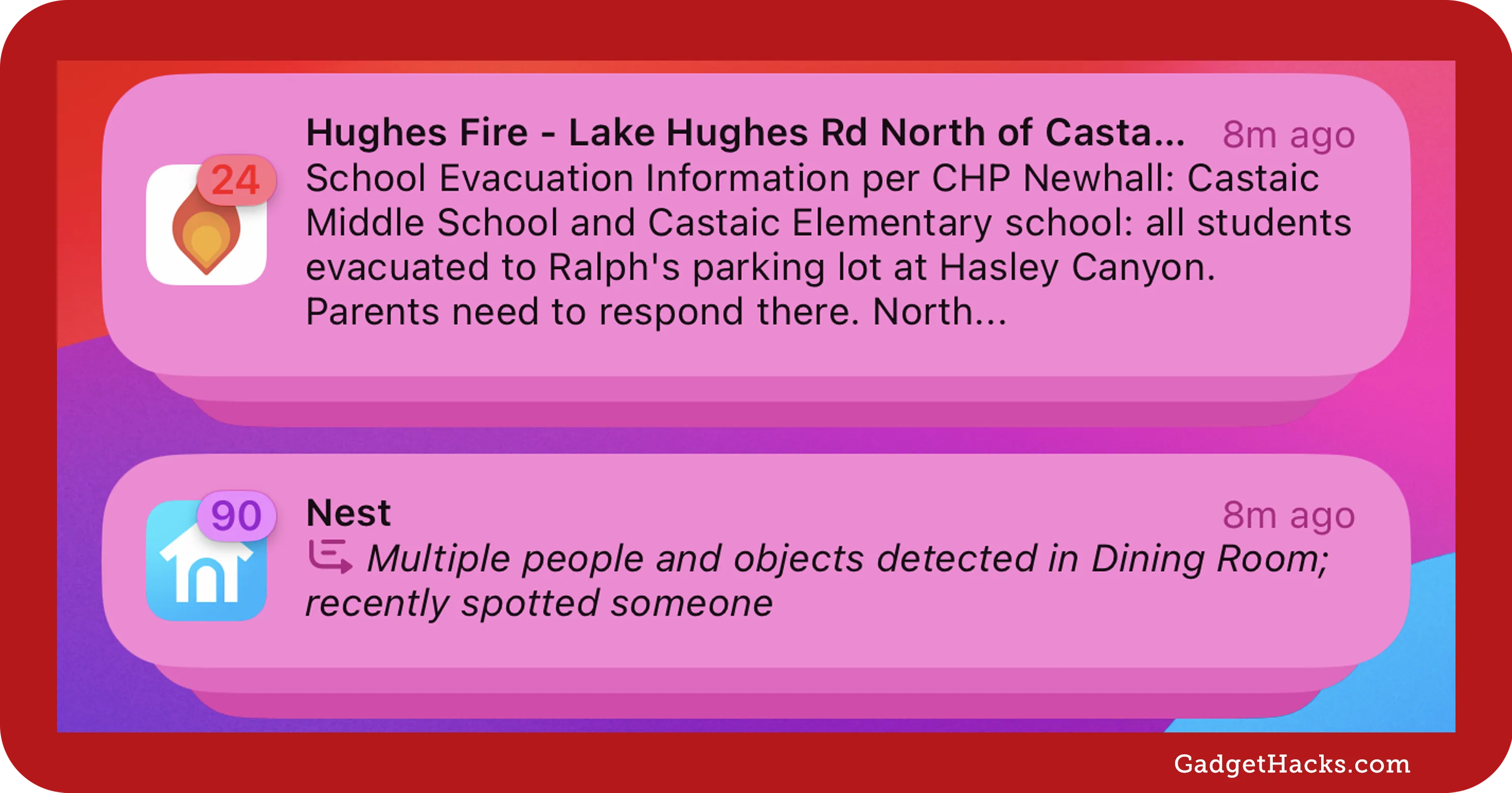
To start, I'll show you what Siri replies back when I ask her to "view contacts" on my passcode-protected iPhone.




As is standard, Siri asks me to unlock my iPhone first by entering the passcode, before I can access my contacts.
Exploiting the Security Flaw
In order to exploit the security flaw in Siri, rather than asking to view contacts, simply say "call". Even without having entered my passcode, the command shows up. Now just tap on it to edit, and enter a couple of letters of a common first or last name, then press Done. As you can you, I used "Ne".




Note:I had to use two letters to reveal the exploit, but the original video shows that it can work with one.
If there are multiple contacts starting with the letters you entered, you will receive a list of names that you can choose from. If only one name shows up, it will place a phone call to that person, so you'll have to try another combination of letters.
Accessing the Contact List
Tap on Other... to see all of the contacts on the iPhone, ready for you to go through and select. Once you have names and phone numbers, you can use Siri to call, email, or message them directly.




While the use for this is limited to prank calling people on your friend's or family's phones, it just goes to show that Apple should spend more time with security issues and improving what they have, rather than spending so much time adding new features to iOS.
How to Protect Yourself
We've had passcode exploits in the past (in iOS 7.0.2), but they're usually patched rather quickly. In the meantime, you can disable Siri from the lock screen by going to Settings -> Passcode and toggling off Siri.

For now, this is just another is a growing list of things that Apple should patch up in the next update.



















Comments
Be the first, drop a comment!