After about 40 days of beta testing, Apple pushed out iOS 11.4.1 to everyone as a stable build on Monday, July 9, exactly one week after the final beta appeared.
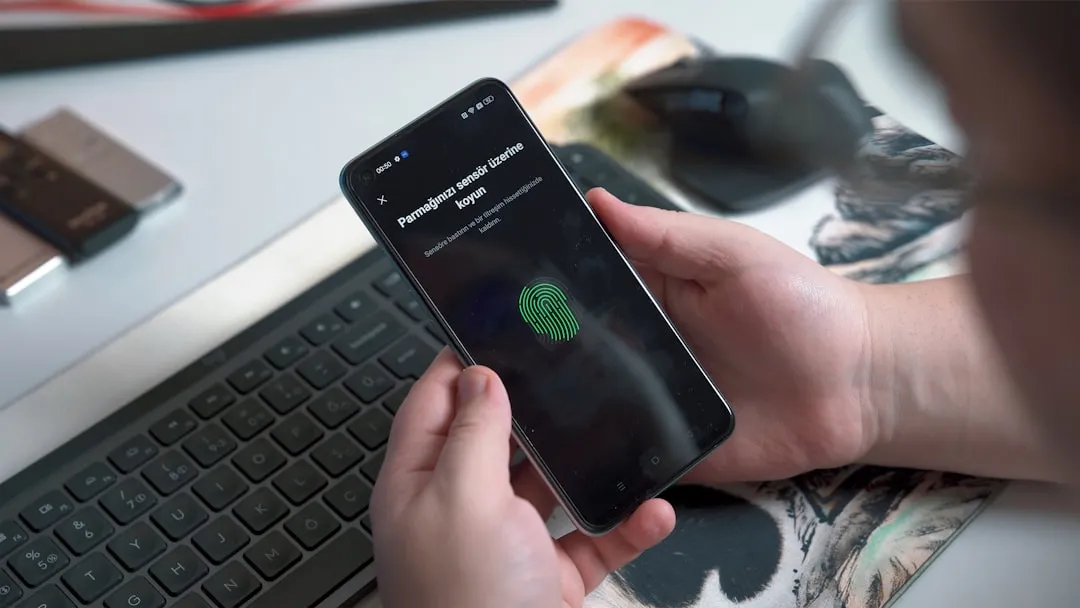
Hidden within the iOS 11.4.1 update is the new USB Restricted Mode that Apple introduced in the iOS 12 beta which renders brute-force tools such as GrayKey and Cellebrite utterly useless. While USB Restricted Mode was released in iOS 11.4, it would take seven days after last unlocking your iPhone for it to lock out all USB accessories. This newer version limits that just one hour.
This shorter time period makes your iPhone more secure but also requires that you unlock your iPhone with a passcode, Touch ID, or Face ID whenever you connect it to your computer to charge or sync with iTunes, but only when it hasn't been unlocking within the last hour. For more details, check out our full guide:




If you're expecting any other new features for your iPhone in iOS 11.4.1, you'll be disappointed because there's nothing else here but bug fixes and security improvements. What those "bug fixes" and "security" improvements are exactly is anyone's guess, since the release notes during the beta did not specify any obvious resolved issues, performance enhancements, or security updates. However, the final release notes state that the following two issues have been addressed.
- Fixes an issue that prevented some users from viewing the last known location of their AirPods in Find My iPhone.
- Improved reliability of syncing mail, contacts and notes with Exchange accounts.
Apple's security updates webpage lists a number of security issues that were addressed on July 9. The issues that were fixed include the following:
- Cookies may have unexpectedly persisted in Safari because of a cookie management issue in CFNetwork.
- Processing an emoji under certain configurations may have led to a denial of service.
- A local user may have been able to read kernel memory because of an out-of-bounds read issue in Kernel.
- An application may have been able to gain elevated privileges from a memory corruption issue in libxpc.
- A malicious application may have been able to read restricted memory from an out-of-bounds read in libxpc.
- Visiting a malicious website may have led to address bar spoofing in LinkPresentation and WebKit.
- A malicious website may have been able to exfiltrate audio data cross-origin via WebKit.
- A malicious website may have been able to cause a denial of service from a race condition in WebKit.
- Processing maliciously crafted web content may have led to an unexpected Safari crash because of multiple memory corruption issues in WebKit.
- Processing maliciously crafted web content may have led to arbitrary code execution because of a type confusion issue or multiple memory corruption issues in WebKit.
- Visiting a malicious website may have led to address bar spoofing because of an inconsistent user interface issue in WebKit Page Loading.
- A malicious application may have been able to break out of its sandbox because of a memory corruption issue with Wi-Fi.
To make sure you're protecting your data as much as you can, it's advised to update to iOS 11.4.1 as soon as possible even if you haven't experienced the AirPods and Exchange issues above since there are plenty of security enhancements and likely more under-the-hood improvements.
To get the update, just open up your Settings app, tap "General," then "Software Update." Once there, follow the on-screen instructions to download and install iOS 11.4.1 on your iPhone. If you were on the iOS 11.4.1 beta and you're on the latest beta version, it's the same version as the public release, so you don't need to worry about getting the final one since you already have it.




In the future, in iOS 12, manually updating to new software updates will be a thing of the past, if you want it to be. A new feature will allow you to set updates to download and install automatically, so you're always on the latest and greatest iOS version. If you want to try that feature out right now (and more), you can join the iOS 12 beta program as a developer or public beta tester.
- Follow Gadget Hacks on Facebook, Twitter, YouTube, and Flipboard
- Follow WonderHowTo on Facebook, Twitter, Pinterest, and Flipboard
Cover image and screenshots by Justin Meyers/Gadget Hacks























Comments
Be the first, drop a comment!